Today I got some time to take care of my server so i installed the latest updates checkt the system for attacks and when I checkt my SSL-certificates i found out, that they were just valid till April 2015 … UPS … ok they are not officially signed and i just use them to encrypt sensitive communication with my server but i wanted to fix that issue and some other little issues i found when checking my blog with https://www.ssllabs.com/ssltest/analyze.html?d=blog.fawcs.info.
Because I also had to regenerate the certificates for my other subdomains I wrote a little script to do that for me (and to use it in the future, because I always have to look up the SSL-certificat generation)
So here is the script:
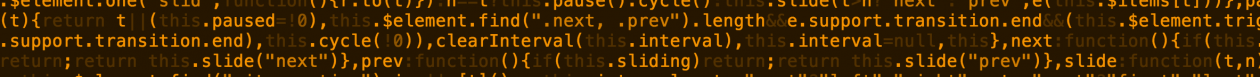
[pastacode lang=”bash” message=”SSL cert-generation” highlight=”” provider=”manual”]
#!/bin/bash
if [ -z $1 ];
then
echo "Parameter 1 for Domain is missing";
exit;
fi
openssl genrsa -out $1.key 2048
openssl req -x509 -new -nodes -key $1.key -days 1024 -out $1.crt -subj "/C=AT/ST=Vienna/L=Vienna/O=fawCS.info/CN=$1"
[/pastacode]
I also updated the security settings in my virtual host configuration files for some settings. The DH-KeyExchange cipher got excluded from the available ciphers because there is a new attack against DH which makes it vulnerable to MITM-attacks.
http://www.heise.de/security/meldung/Logjam-Attacke-Verschluesselung-von-zehntausenden-Servern-gefaehrdet-2657502.html [German]
Extract of settings:
TraceEnable off
ServerSignature Off
ServerTokens Prod
SSLProtocol all -SSLv2 -SSLv3
SSLHonorCipherOrder on
SSLCipherSuite “EECDH+ECDSA+AESGCM EECDH+aRSA+AESGCM EECDH+ECDSA+SHA384 EECDH+ECDSA+SHA256 EECDH+aRSA+SHA384 EECDH+aRSA+SHA256 EECDH+aRSA+RC4 EECDH !EDH+aRSA !RC4 !aNULL !eNULL !LOW !3DES !MD5 !EXP !PSK !SRP !DSS”
And it’s always a good idea to to use htaccess with extra users or IP-ACLs to secure specific directories. (for example the wp-admin directory 🙂 )
Some other interesting settings to macke apache more secure can be found her: http://www.tecmint.com/apache-security-tips/